Subscribe to our blog
LashHacks: Exporting ComplianceMonitor Emails to Save Offline
Jan 26, 2024
This Month’s Hack: Exporting ComplianceMonitor Emails to Save Offline Did you know that you can easily export a CSV list of emails with compliance issues…
Blog
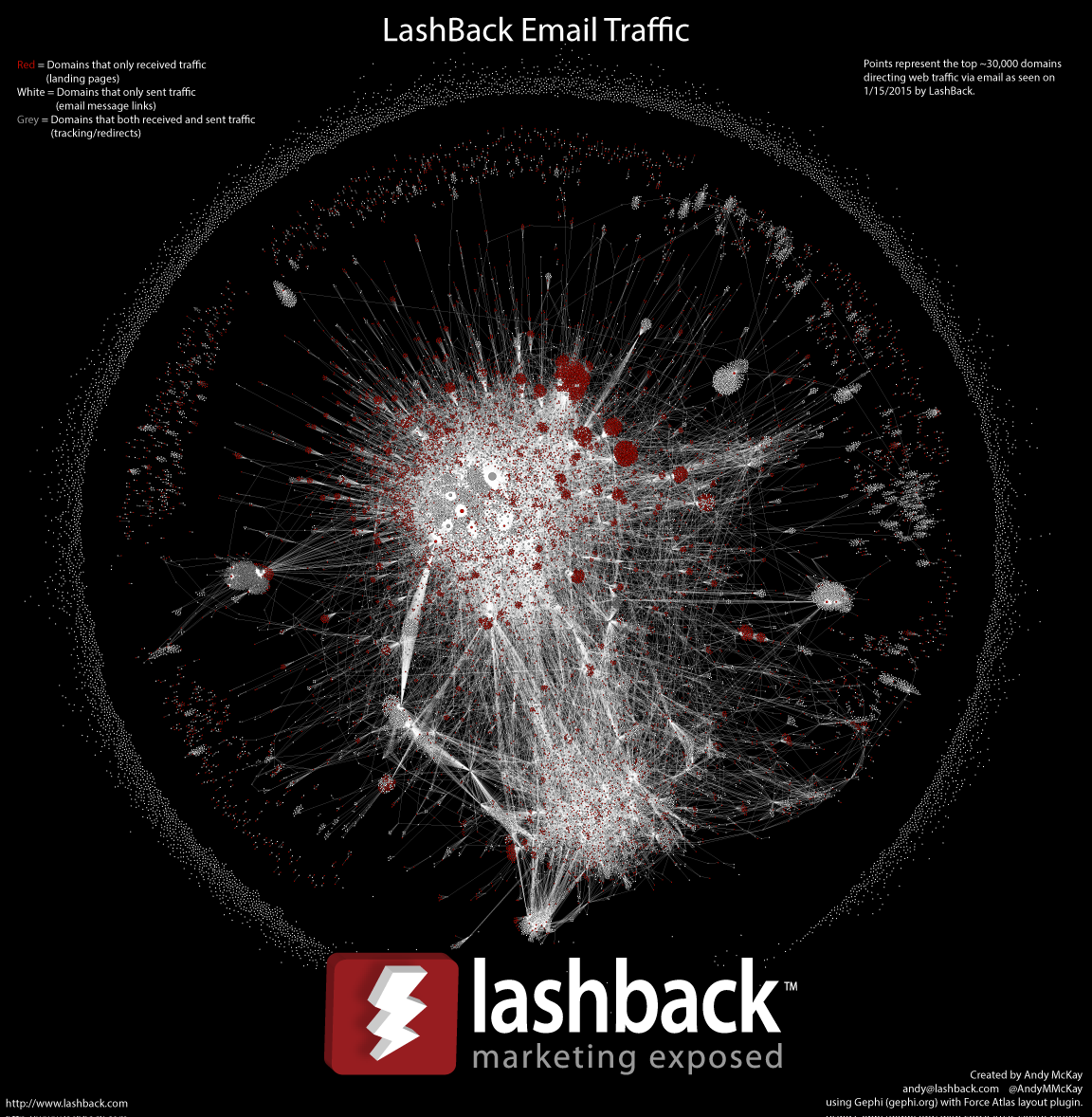
A unique, time-tested solution that addresses a critical need for advertisers, agencies and networks.